West Virginia State University - Marquis Who's Who Selects Eric L. Jackson for Success in Higher Education Administration

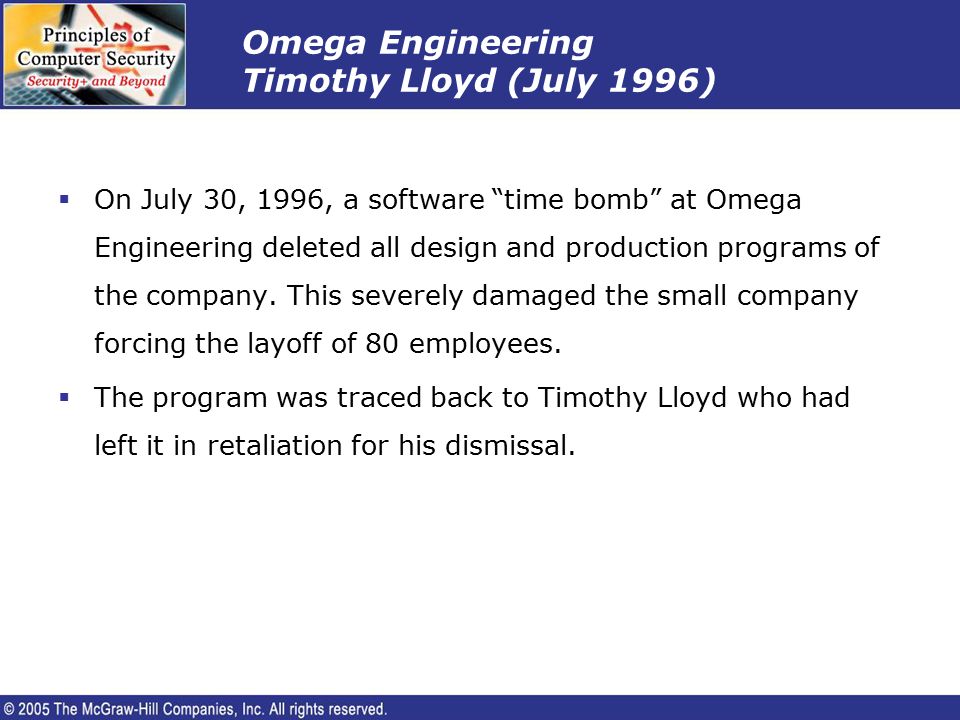
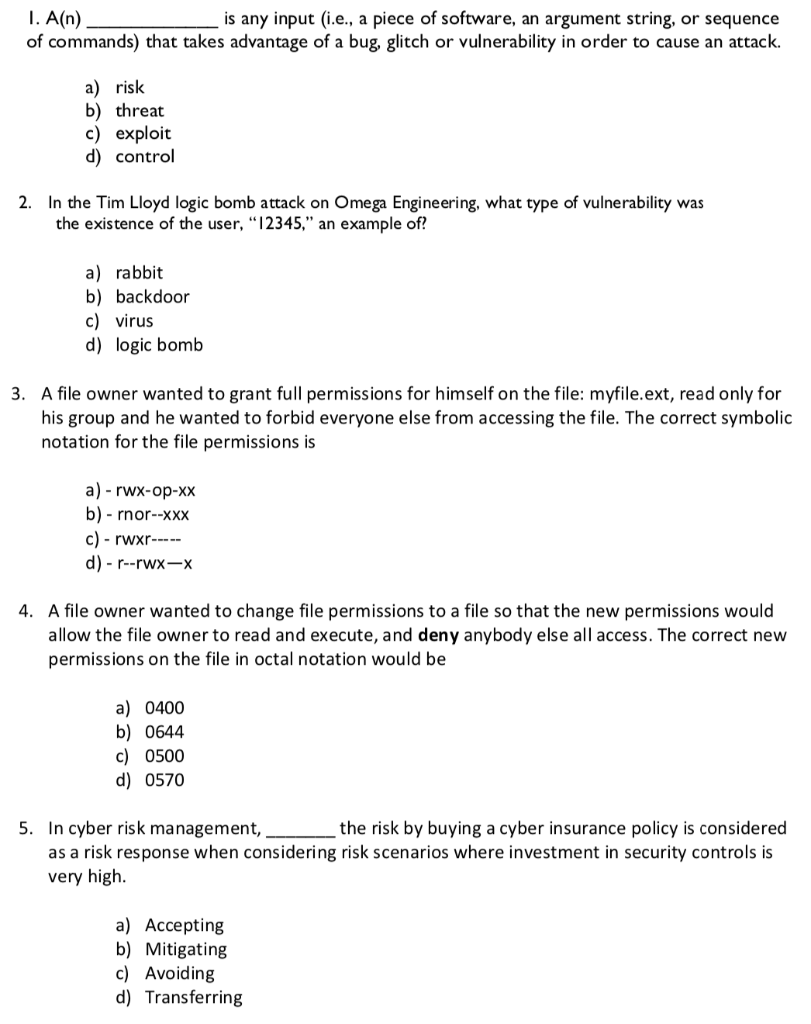
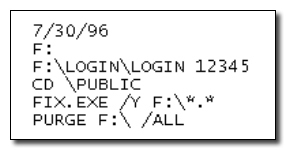
In the Tim Lloyd logic bomb attack on Omega Engineering, what type of vulnerability was the existence of the user "12345" an example of? | Homework.Study.com