Password Hashes — How They Work, How They're Hacked, and How to Maximize Security | by Cassandra Corrales | Medium

Small 75u sample from my first bubble hash attempt. Used a freezer and a microplane. My buddy was in the stars last night so I guess it turned out okay. : BubbleHash

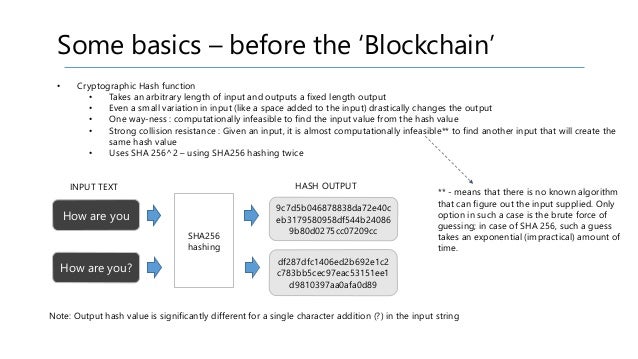
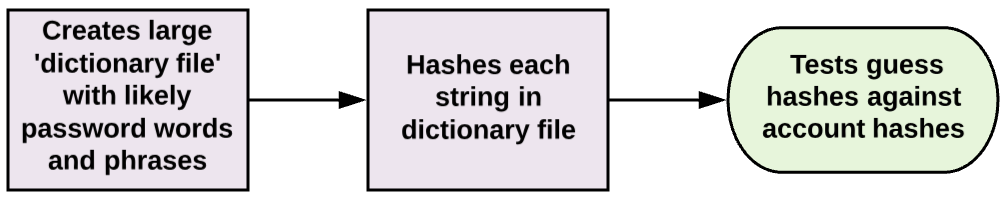
Password Hashes — How They Work, How They're Hacked, and How to Maximize Security | by Cassandra Corrales | Medium

I ordered hash browns with cheese at Waffle House, I guess they technically delivered. : shittyfoodporn