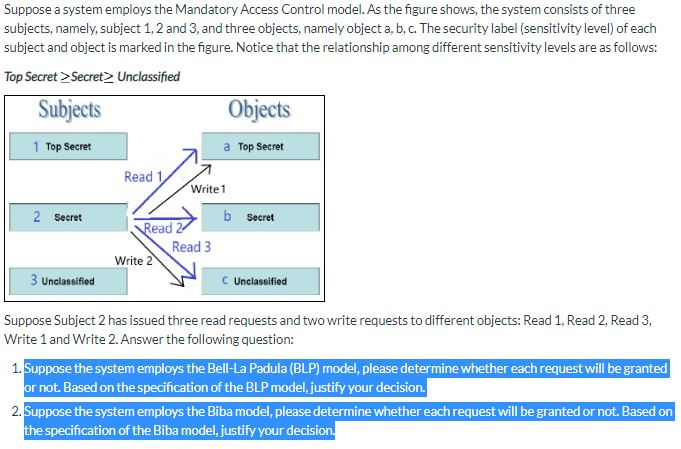
Discretionary Access Control vs Mandatory Access Control - Part 2: Mandatory Access Control Fundamentals

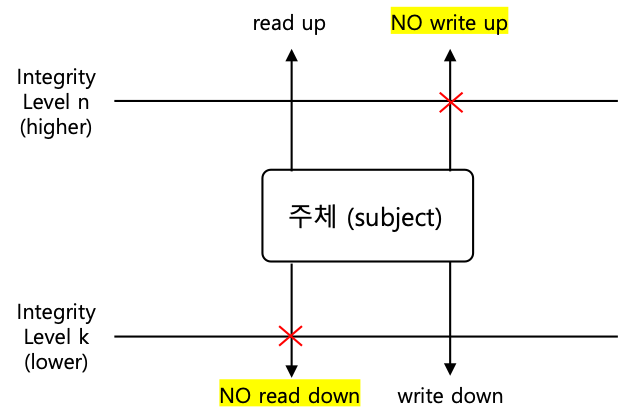
Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram
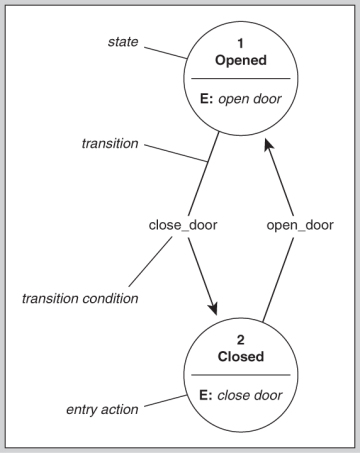
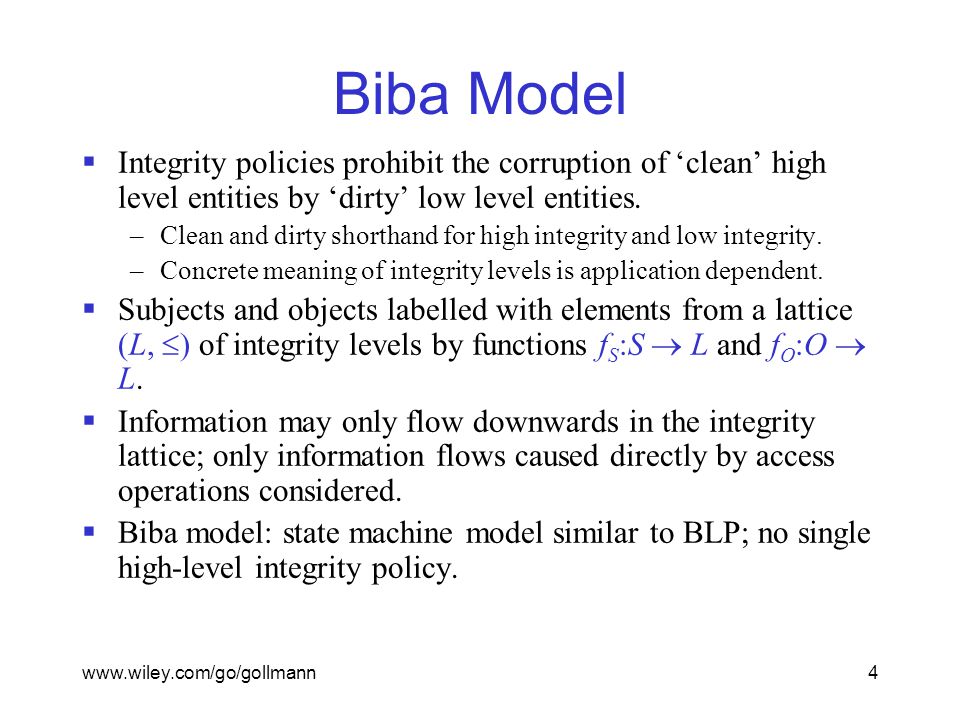
Integrity Models Biba Integrity Model (1977) Biba Model – ”no read down” Biba Model – ”no write up” Biba Model – i
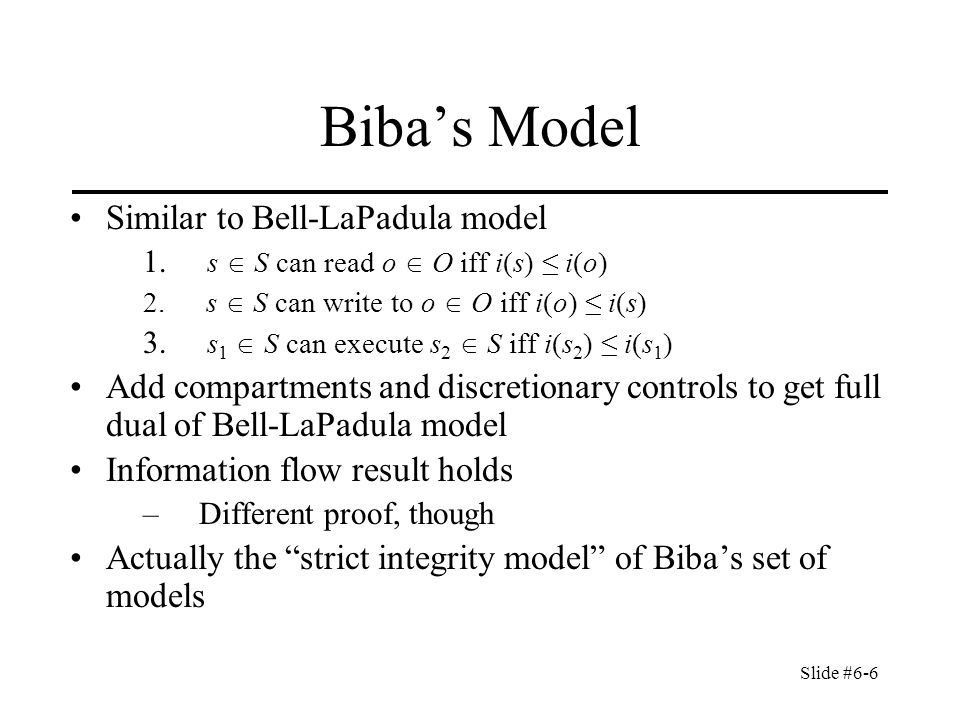
Slide #6-1 Chapter 6: Integrity Policies Overview Requirements Biba's models Clark-Wilson model. - ppt download